News
.jpg)
February 3, 2026
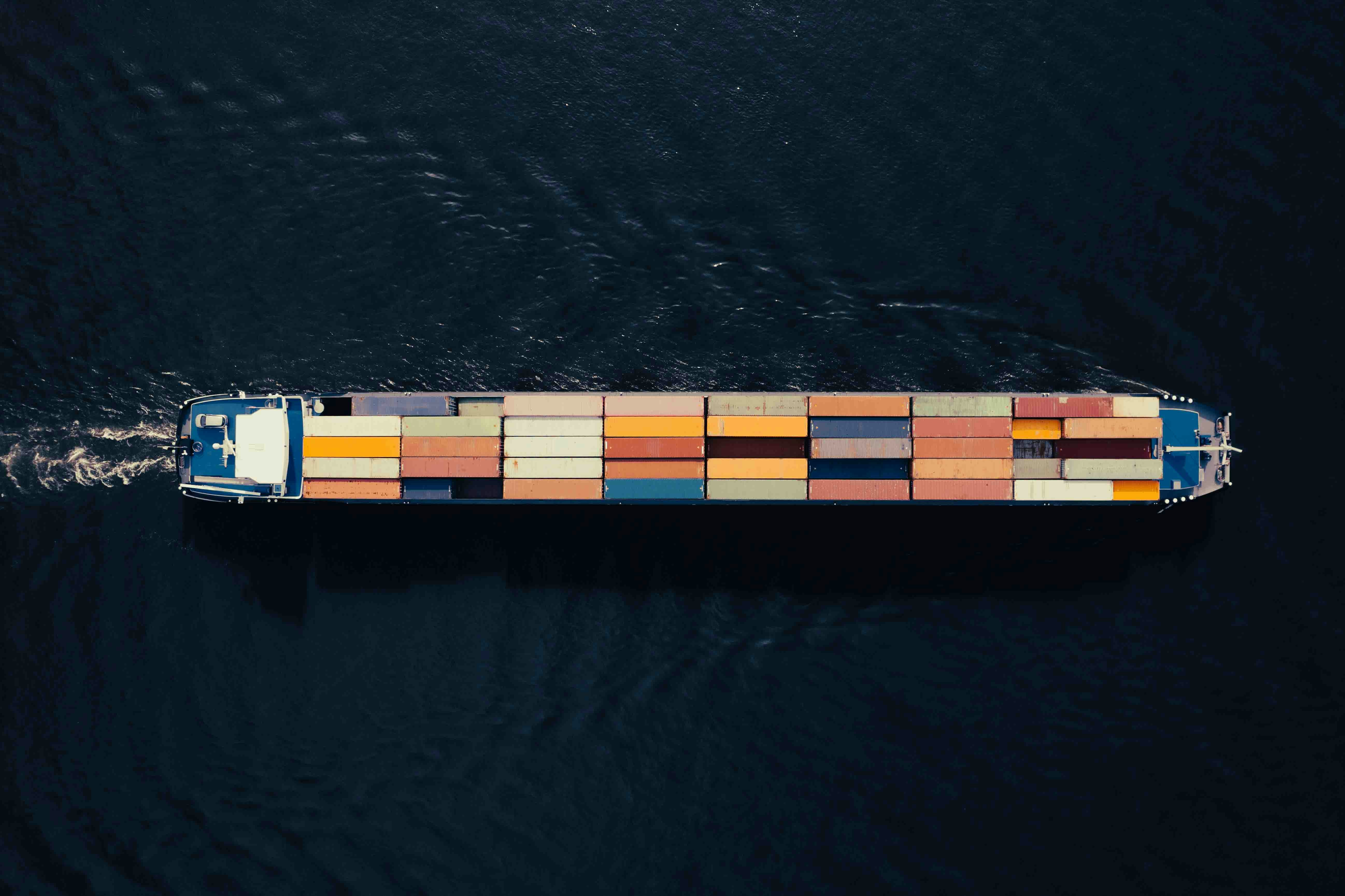
Cybersecurity in the Supply Chain: How attackers infiltrate your business relationships
Supply chain attacks exploit updates, access rights, APIs, and identities. A practical guide to real attack paths and immediate cybersecurity measures that work.
















%20(1).png)

